TEST-X
Immobilizer
The Immobilizer feature provides an additional layer of vehicle security by requiring driver authorization after the ignition is turned on. It is designed to block the vehicle's starter circuit, preventing the engine from being started until an authorized identification element is presented.
This functionality is essential for preventing vehicle theft and ensuring that only permitted individuals can operate a vehicle. By linking vehicle operation to a physical token, it significantly enhances security for fleet management, rental services, and any application where control over vehicle access is a priority.
The feature operates based on the vehicle's ignition status. When the ignition is turned on, the system enters a "Waiting authorization" state, activating a digital output to keep the starter blocked. Upon successful presentation of an authorized element, the system transitions to an "Authorized" state, deactivates the output, and allows the engine to run. The authorization is automatically revoked after the ignition has been off for a configurable period.
Prerequisites and Important Settings
- The vehicle's ignition status must be monitored by one of the device's digital inputs (DIN).
- A relay must be correctly installed to interrupt the vehicle's starter circuit and connected to one of the device's configurable digital outputs (DOUT).
- An iButton reader is required to detect the authorization element.
- The unique IDs of all authorized iButtons must be pre-configured in the device's authorization list.
Basic Operation
The feature's logic is managed through three distinct states:
1. Not Authorized State:
- This is the default, idle state when the vehicle's ignition is OFF. The immobilizer is armed and waiting.
2. Waiting Authorization State:
- When the ignition is turned ON, the system transitions to this state.
- If a Digital Output is configured, it is immediately activated to control the relay and block the starter circuit.
- The device actively waits for an authorization element to be presented.
3. Authorized State:
- Once an ID is detected and confirmed to be authorized, the system transitions to the Authorized state.
- The configured Digital Output is deactivated, which unblocks the starter circuit and allows the vehicle to be started and driven.
- The driver remains authorized as long as the ignition stays ON.
4. De-authorization Process:
- When the ignition is turned OFF, a de-authorization timer begins.
- If the ignition remains off for the entire duration of the configured "Authorization persist duration", the system revokes the authorization and returns to the Not Authorized state. If the ignition is turned back on before the timeout expires, the authorization remains active.
5. Authorization list management:
1-Wire
- If no 1-Wire authorization list is used, any ID can be used for authorization.
- If 1-Wire authorization list is used, device will allow authorization only by specifics IDs. Authorization list management can be done in (Accessories) section of the TCT, the user can upload, preview and delete a .csv file with up to 10000 device IDs. ID format will be string of 8 bytes in hex format, e.g: AABBCCDDEEFFAABB. It is also possible to manage 1-Wire authorization list via FOTA using task type: Upload 1-Wire authorization list / Receive 1-Wire authorization list.
BLE Sensors
- If no BLE device authorization list is used, any ID can be used for authorization.
- If the BLE authorization list is used, the device will only allow authorization from specific BLE devices whose MAC addresses are included in the list.
The authorization list can be accessed in the Immobilizer window, where the user can upload, preview, or delete a .csv file containing up to 200 BLE device entries.
- Each BLE device ID must be provided as a Bluetooth MAC address in the following hexadecimal format:AA:BB:CC:DD:EE:FF
- Any BLE device can be used for authorization — not only Teltonika EYE sensors.
Authorization is performed exclusively by checking the Bluetooth MAC address.
NOTE:
It is also possible to manage the Beacon authorization list remotely via FOTA using the following task types:Upload Beacon authorization list and Receive Beacon authorization list.
NOTE:
Example files are provided to illustrate the correct structure for uploading authorization lists. The included ibutton_list.csv and File:Bluetooth mac list.zip files demonstrate the required formatting for 1 Wire and Beacon (BLE) entries.
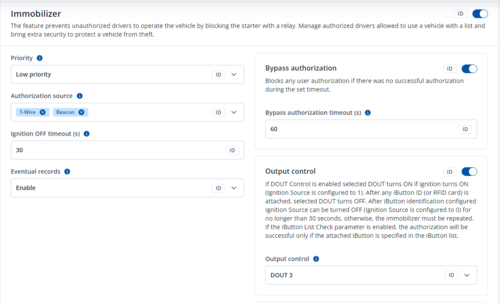
Parameters list
| PARAMETER NAME | PARAMETER ID (RELATED AVL ID) | DESCRIPTION | VALUES |
|---|---|---|---|
| Immobilizer | 1024800 (248} |
Disables, or enables and sets priority of the event record generated upon successful or failed authorization attempts.Authorization source | 0 = Disable scenario. 1 = Low priority Device makes an additional record with indication of event cause. |
| Authorization mode | 11703 | Selects singular or multiple types of authorization elements to be used. | 0 = No authorization selected. 1 = 1-Wire authorization selected. Driver is authorized via iButton or RFID tag. |
| Authorization persist duration (s) | 60068 | Sets the time in seconds after the ignition is turned off before the driver's authorization is automatically revoked. | Minimum value = 1 Maximum value = 65535 |
| Bypass authorization | 11029 | Allows to bypass authorization when ignition is turned on and a set duration expires. | 0 = Disabled 0-65535 = Enabled |
| Bypass authorization timeout (s) | 11029 | Sets duration which starts when ignition is turned on. When duration expires immobilizer is turned off, even if the user was not authenticated. | Minimum value = 1 Maximum value = 65535 |
| Output control | 11702 | Selects which Digital Output is used to control the immobilizer relay. | 0 = None DOUTs are disabled in this scenario. 1 = DOUT1 DOUT1 is enabled in this scenario. |
Limitations, Edge Cases & Additional Notes
- Installation Security: The overall effectiveness of the immobilizer is highly dependent on the secure and discreet installation of the control relay. If the wiring is easily accessible, it can be bypassed.
